Security researchers have detected a big malware campaign that is using fake websites to impersonate popular products and brands to spread malware. So-called typosquatting attacks register domain names that resemble the domain names of legitimate products. Many times, only a single character is different, added or removed from the domain name.
While observant Internet users may spot the fake site by looking at the domain name, many rely on visual elements of the site instead to judge its authentiticy.
The campaign uses at least over 200 typosquatting domains to impersonate 27 brands, including TikTok, Figma, PayPal, SnapChat, APK Pure, Google Wallet or Microsoft Visual Studio Code.
Originally detected by cyber-security firm Cyble, the company believed that the campaign was targeting Android primarily by creating fake sites to download Android APK files. Our colleagues over at Bleeping Computer discovered that the campaign extends beyond Android, as it targets brands in software, cryptocurrency and other niches as well.
Even popular open source programs, such as Notepad++, Thunderbird or Tor Browser, are among the impersonated brands. Some domain names look very similar to the original and most websites look like exact replicas of the original sites.
The campaign spreads different types of malware. Bleeping Computer found the info-stealing malware Vidar Stealer on a fake Notepad++ site, and the Agent Tesla keylogger and RAT on a site impersonating the Tor Project website.
The malicious sites are spread using various methods, including by email, by accidental typos from users, and other means, which may include via chat messages, social sites or by SMS.
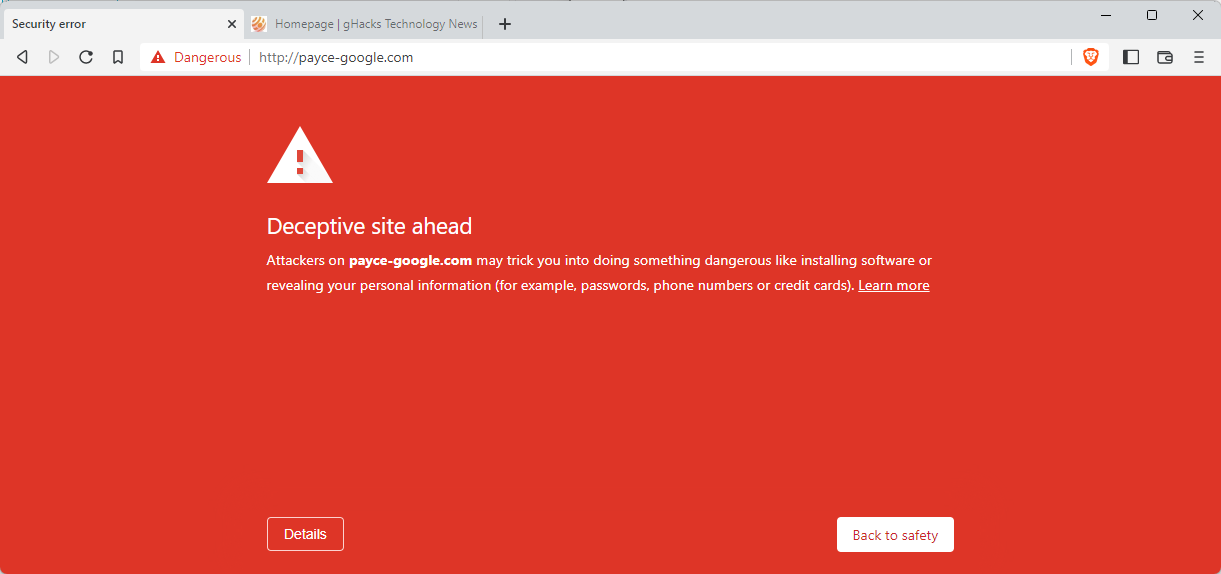
Most sites should be blocked in modern web browsers by now. An attempt to open them in a browser should display a security warning. There is the chance, however, that new sites are created that are not yet blocked.
The main protection against these type of sites is to check the address of the site before interacting with it. It takes just a second or two to check the URL of the site and determine whether it is the real site or not. If users do not know the real domain, they may use search engines to find the right homepage. Sometimes, local data may also help in identifying the correct website.
It is also a good idea to avoid clicking on any links in emails and on social sites.
Now You: do you check website addresses before interacting with them?
Thank you for being a Ghacks reader. The post Massive Fake Website Campaign Spreading Malware detected appeared first on gHacks Technology News.
